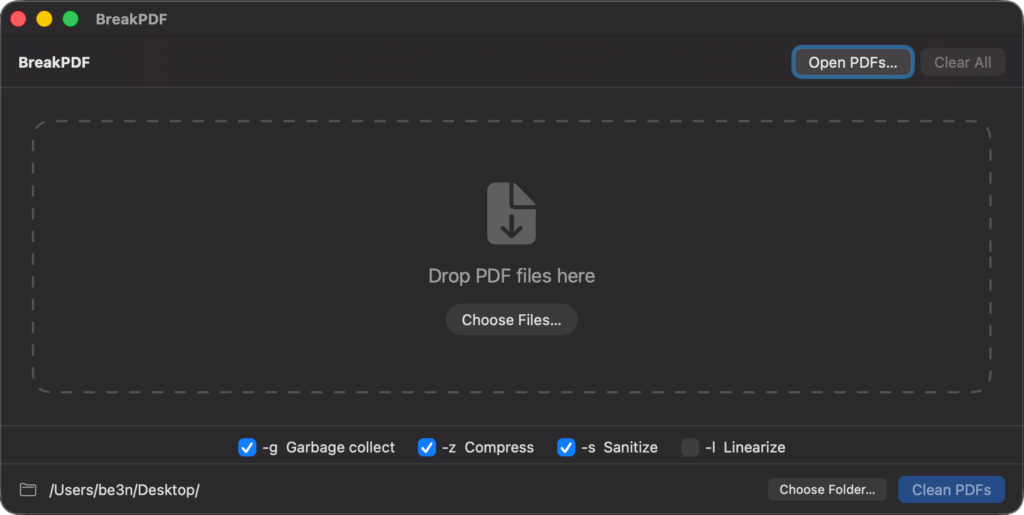
Long awaited and much needed update to my breakPDF application!
Ages ago, i built a php app for processing pdfs made of mupdf. i even made a go at a MacOS version. it was never very good and it broke with MacOS updates. This new complete rewrite now available! enjoy.
Product page can be found here.
Checking out Hummingbird Trail in Simi Valley.
Continuing my exploration these hills, i found another trailhead. This time in Simi Valley and despite a understated entrance, we found some exciting features. Including this wash under the 118! Respite from the sun and incredible acoustics. There was a cave that none of the trails we found seemed to head towards. We met another hiker who gave us an idea of how to find it. Next time.
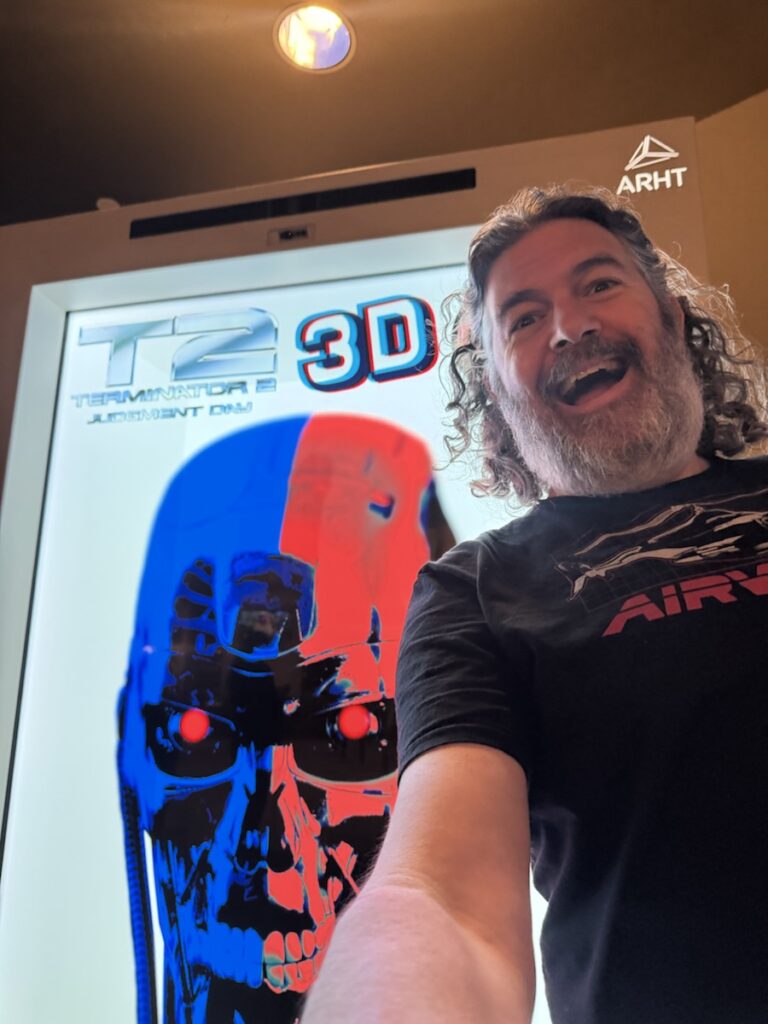
Maurice LaMarche & Cary Elwes Discuss The Princess Bride!
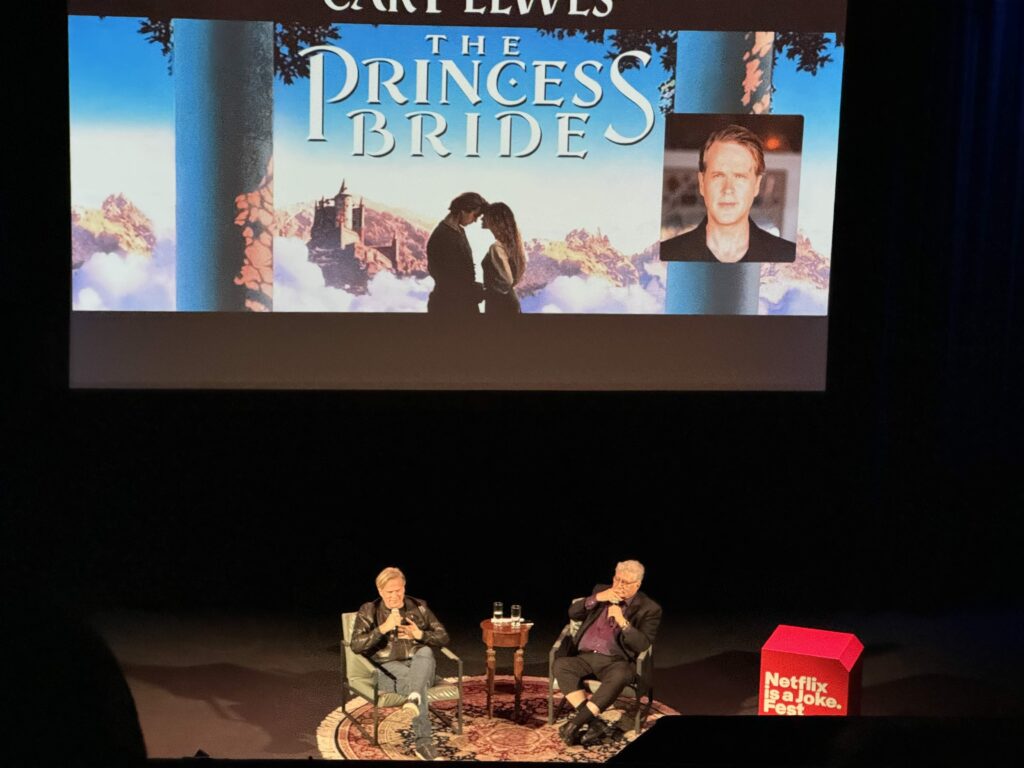
This was and awesome surprise invite from a friend. I have loved this film from my first viewing. i own it on VHS, DVD, and Laserdisc! The Princess Bride screening at Ebell Theater with Q & A with Cary Elwes moderated by Maurice LaMarche. Incredible stories told with the unbelievable voices of the film’s cast and crew performed by Cary. Cary was promoting his book, As You Wish: Inconceivable Tales from the Making of The Princess Bride. Download the audio from the Q & A here or play it bellow.
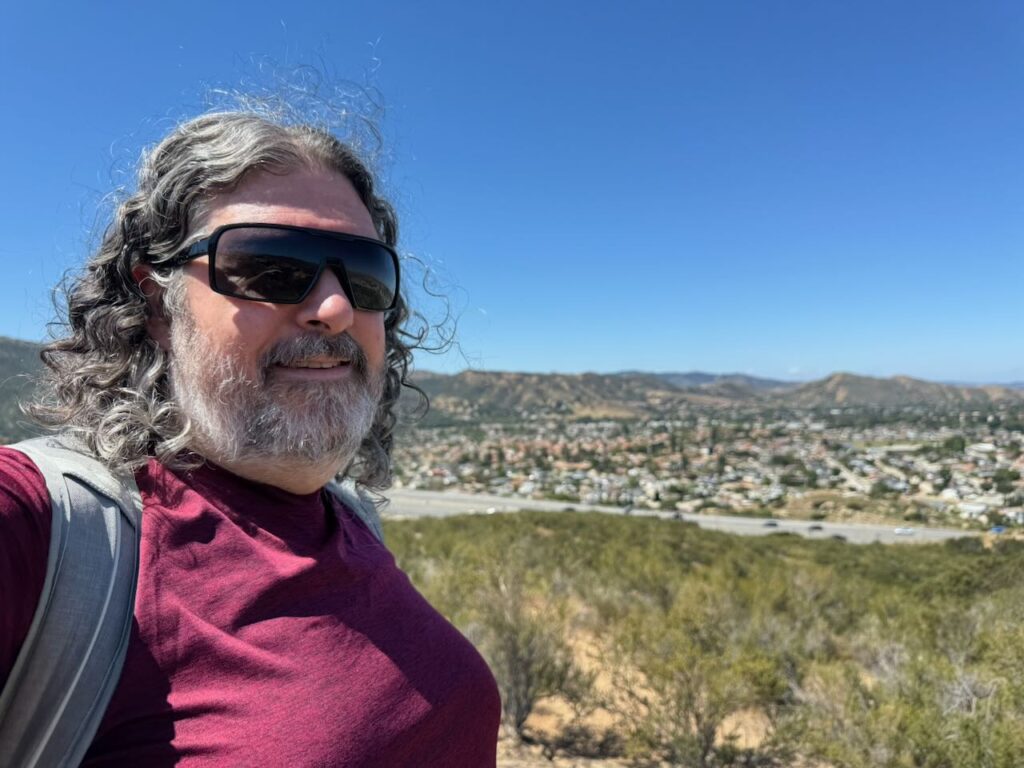
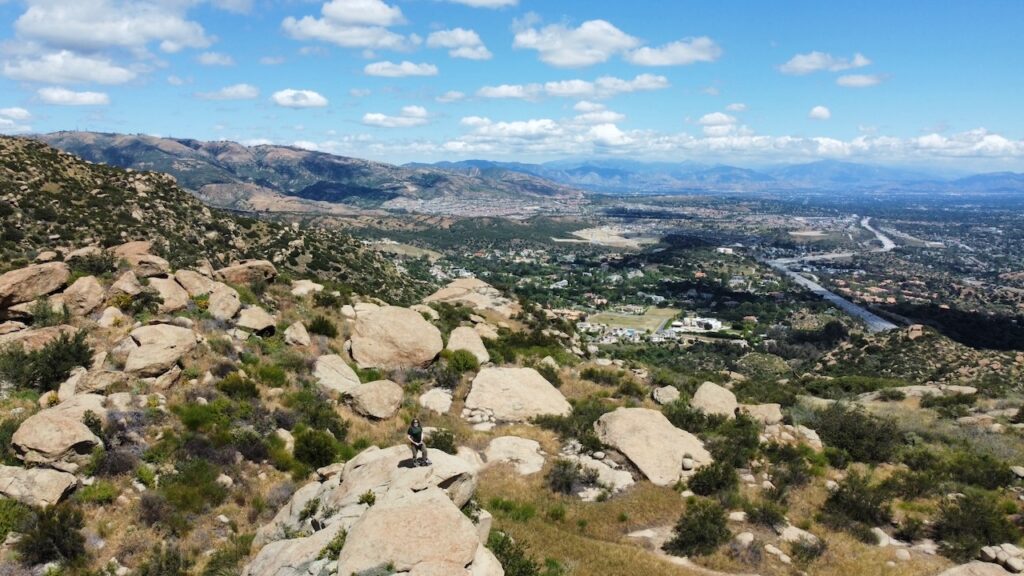
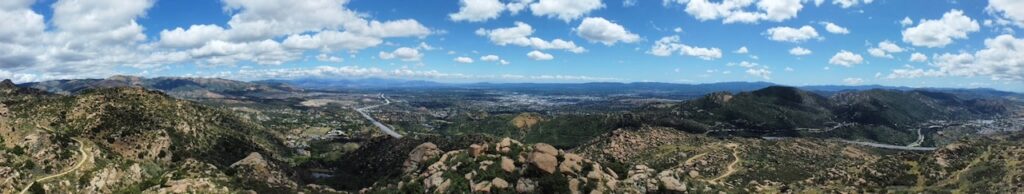
Rocky Peak trail on a beautiful day!
The weather was amazing and my work was canceled so i went on an adventure! i’ve been to Stony Point and Vasquez Rocks dozens of times, but i’d never been on this trail. From clouds to the flowers, it was a glorious hike.
Enjoy these images. I shot so many panoramas, it was hard selecting these.
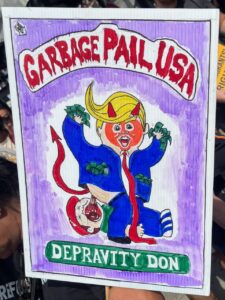
No Kings 3! This time downtown!
My first No Kings protest downtown and it was exciting. Live performance, crazy characters, great signs and lots of camaraderie. i gave out stickers and made friends as we idled and marched. Unlike the first and second march, this time i traveled to downtown los angeles to participate in a much larger gathering. i couldn’t get pictures of all the incredible costumes. Everyone was so friendly and curious. i lost count of how many times i bumped into or stepped on the foot of a fellow protestor.
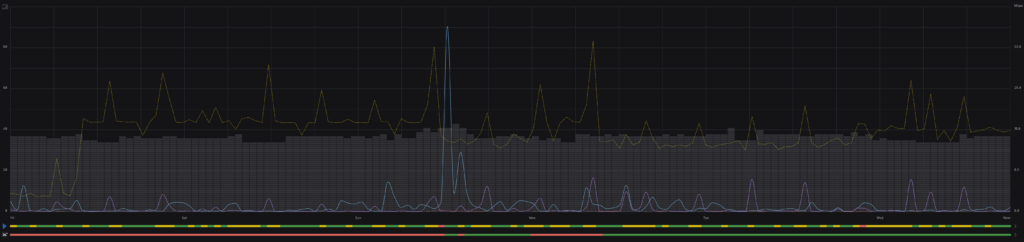
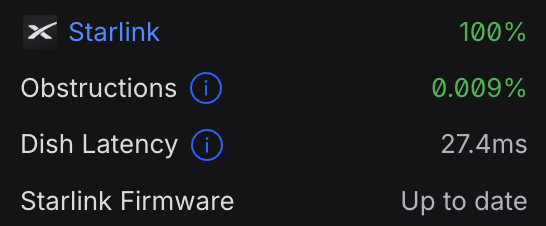
Dual WAN fully engaged!
This is was a long time coming. i’ve had the equipment for years, but it was always needed elsewhere. Finally home, it’s up and running. smoother and more reliably than with any previous deployment. Just in time for me to accidentally unplug my Spectrum modem!
I was surprised and impressed by the integration with the Starlink that Unifi exhibited. including obstruction info and firmware info on the Unifi dashboard.
VCF 2026! give away all the things and maybe get a few more
 It’s that time of year again, and the Vintage Computer Festival. When i clean out my garage and marvel at all the incredible past computing and electronics that are kept working with love and proficient attention to maintenance. not my first visit, or even my second.
It’s that time of year again, and the Vintage Computer Festival. When i clean out my garage and marvel at all the incredible past computing and electronics that are kept working with love and proficient attention to maintenance. not my first visit, or even my second.

 This year i brought three carloads, with xServes, xRAIDs, and fiber channel gear! Time Capsules in original packaging. iMacs and laptops from many generations and many operational statuses.
This year i brought three carloads, with xServes, xRAIDs, and fiber channel gear! Time Capsules in original packaging. iMacs and laptops from many generations and many operational statuses.


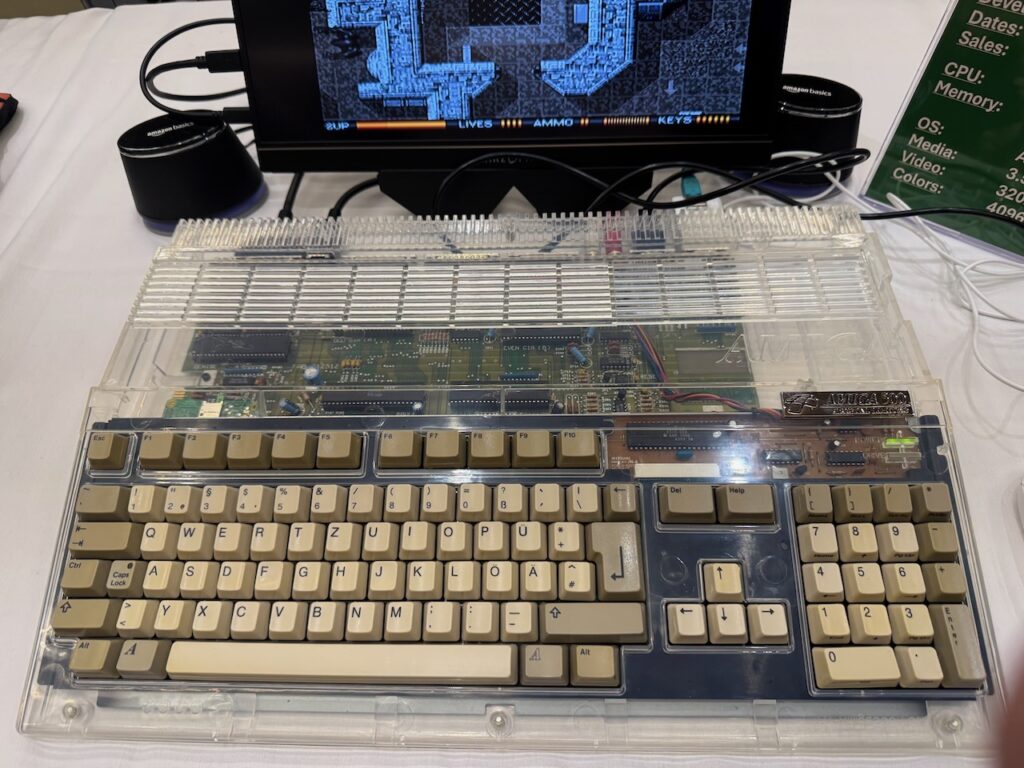
 There was a demo of adult themed “dirty” original nintendo games. i never knew. custom cases, or custom lights, here was an Amiga 500 made clear. looking good.
There was a demo of adult themed “dirty” original nintendo games. i never knew. custom cases, or custom lights, here was an Amiga 500 made clear. looking good.
Two of my dream systems were in the consignment room. i was proud that i didn’t go home with a 20th Anniversary Mac nor a MacTV. it was hard, but had to be done.