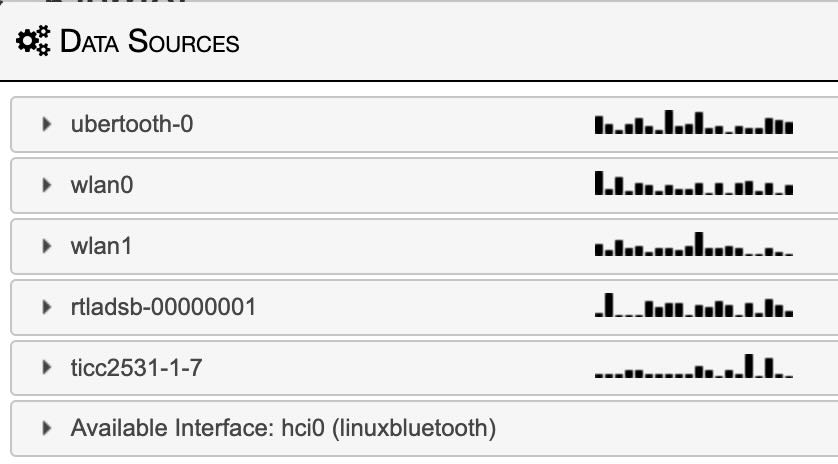
 Launched at Defcon 33 and eagerly awaited by wifi tinkerers and technologists. i finally received mine. i’m still figuring out the functionality from potential. As a handheld device, unlike the rest of the pineapple line, it is designed to be used from the device. i was looking for an always monitoring device with audio and haptic alerts. it’s handheld nature makes extracting logs a novel concept, but it is already providing insight into my wireless space.
Launched at Defcon 33 and eagerly awaited by wifi tinkerers and technologists. i finally received mine. i’m still figuring out the functionality from potential. As a handheld device, unlike the rest of the pineapple line, it is designed to be used from the device. i was looking for an always monitoring device with audio and haptic alerts. it’s handheld nature makes extracting logs a novel concept, but it is already providing insight into my wireless space. 
 I love the default look with all it’s retro elements. From war games to classic MacOS, out of the box it has more retro style than it’s 90s pager reveals. it operates on 3 wifi bands! (2,5,6) and maybe bluetooth as well eventually. This is just the beginning as the firmware gets more mature and additional content is added by the users. this is with the stock hardware. Hak5 is already selling USB modules for ethernet, GPS, and LoRa for even more functionality. i’ll update as i get more capable with the gadget. currently it does eat it’s battery very enthusiastically. i don’t think i’ve gotten more than 2-3 hours of use on a charge. (but i don’t yet know what i am doing)
I love the default look with all it’s retro elements. From war games to classic MacOS, out of the box it has more retro style than it’s 90s pager reveals. it operates on 3 wifi bands! (2,5,6) and maybe bluetooth as well eventually. This is just the beginning as the firmware gets more mature and additional content is added by the users. this is with the stock hardware. Hak5 is already selling USB modules for ethernet, GPS, and LoRa for even more functionality. i’ll update as i get more capable with the gadget. currently it does eat it’s battery very enthusiastically. i don’t think i’ve gotten more than 2-3 hours of use on a charge. (but i don’t yet know what i am doing)
Category: Security
Back from Defcon 32 with knowledge swag but no voice
I had a great time this year. i went deep into the sticker game and spent WAY too much time playing with the badge. Playing with the badge allowed me to meet and work with some incredible people with whom we learned, laughed, and lamented the badge’s terrible supplied SD cards. This year i brought flyers to promote my phone adventure game and joined in #StickerLife with a supply of stickers of my own. unfortunately the printers gave me too many flyers, but not enough stickers.
My game did get some traction this year for the first time. Still no winners, but i did get this incredible voicemail from one of the players. I appreciated more ridiculous phone stuff. great job whoever you are! EDIT: i think i found you Foxbox!
The Badge had a lot of problems. only some of which were patched with updates. I excitedly made changes, but then the SD card would fail and be unable change back. currently mine is stuck as a Mario Game, which is not so terrible. i can finish the Defcon GameBoy game on an emulator.





The antennas are back! Wardriving in a Tesla.

This project was cannibalized over a year ago. With Raspberry Pi as difficult to get ahold of as they’ve been, i thought this project might never come back to life. I launched a number of pi liberating ideas with some success. I now have enough for both fun personal projects and to get my work done. I felt i should explain the name wardriving. It is a variation on wardialing. Wardialing was trying phone numbers, looking for interesting things on the phone. Wardriving is similarly driving around looking for interesting things in the air.
My wardriver is not pictured above, but these Pi are ready for whatever comes next. I’ve recovered an assortment of different Pi from original B+ (pi-hole) to a 2GB Pi 4 (broken helium miner). One of the best parts of this setup is the early Pi 3 (not B+). This was a lucky find as it consumes less energy and produces much less heat. With only 6 radios running (including GPS) the lower performance hasn’t been an issue, but the reduced power has been incredible. Early testing has me getting an additional 20-40% battery life vs the original pi 4 configuration. my cable management has also improved with this iteration. The setup fits in a small box in my trunk instead of a tangled mass of wires in a large bin (prototyping is fun). The reason power is so important because, believe it or not, the amperage you can pull out of a Tesla for accessories is limited. Without an alternator dumping piles of unclean energy i am forced to resort to BYOB (bring your own battery). I got a monster battery to power the Pi 4 and even more radios and accessories of the original prototype.
It is fun using the ADSB live tracker in Los Angeles as there are always planes above. Next step will be DJI drone tracking and some sort of dashboard indicator/control. I started a WiGLE account, it’s off to a pretty good start. i found a few APs, but i’m still figuring out how to share BT. maybe i’ll join the #HardHatBrigade group.




acme.sh is the ultimate DNS/SSL toolset! i have wasted my life!
I’ve been automating SSL renewals for almost as long as i’ve been deploying them. for the most part, it is very smooth and easy to do. (thanks mostly to certbot and the hard work over at let’s encrypt) The trouble comes up with non publicly addressable servers and other custom setups. cough cough. . . Unifi. . . cough cough.
I recently discovered a tool that makes all those complicated setups as easy as the original certbot installs. acme.sh is that tool. two lines! not since screen have i regret any time i spent not using such a tool.
./acme.sh –renew -d “unifi.domain.com”
./acme.sh –deploy -d “unifi.domain.com” –deploy-hook unifi
Pro Tools users struggling with plugin licenses after activation try this. . .
Users of Antares plugins, or others using Codemeter license manger may be locked out of their licences in Pro-Tools. The licenses show up in the various license managers, but Pro-Tools says NO. This is due to added file system security of Mojave. Add Pro Tools to the “Full Disk Access” list in Security & Privacy System Preference. That should solve the problem. good luck.
@defcon just retweeted me!
In a tweet by @todayininfosec we were all reminded of this day in 1999 when @Dildog and the cDc crew presented Back Orifice 2000 (BO2K) to a delighted crowd at Defcon 7. It was quite a show complete with music, projectors, lights, lasers, and even a Speak-n-Spell. It was a lot of fun, and i was elated to be there. i replied early with my memories, but then i remembered that i had found some photos while cleaning. . .so i posted them. These were film prints from an instamatic (as was the style at the time), so they didn’t come out great! they do offer a tiny keyhole through which we may peer into the past. i am glad it is bringing joy. Then @defcon (the official conference account) retweeted. *blush*
Defcam 2.0 Preparation and more from Defcon 27!
So I did not “complete” my hat until very late Friday when i finally got it to announce its link status on its new set of 14 segment displays. It performed admirably all weekend. Thanks to Paul for safely transporting it to and from Vegas. I must also thank Stephen for his late night help on Wednesday. (tacos are not enough) Without his amazing soldering, i’d still be trying to figure out what i had done wrong. Here are some pictures from that night and the con to follow. . .










Status update:
I’m back in Vegas for Defcon and it’s going swimmingly. so much so that i might get some actual swimming in.
 Thanks to the late night help of Professor Franklin i have improved and redeployed the Defcam!
Thanks to the late night help of Professor Franklin i have improved and redeployed the Defcam!
New security updates overtake jailbreak advantages.
 There are just so many privilege escalation fixes in the latest iOS 12.2 update. I finally removed the jailbreak from my primary device and updated. Privilege escalation is when an unprivileged or user process (like an app from the app store or even a web page*) gets root or even kernel authority. This is when bad turns to worse because it can do and see anything with any of the device’s data or sensors. Since even the big trusted apps have been caught tracking or stealing data, I simply couldn’t leave myself unprotected any longer.
There are just so many privilege escalation fixes in the latest iOS 12.2 update. I finally removed the jailbreak from my primary device and updated. Privilege escalation is when an unprivileged or user process (like an app from the app store or even a web page*) gets root or even kernel authority. This is when bad turns to worse because it can do and see anything with any of the device’s data or sensors. Since even the big trusted apps have been caught tracking or stealing data, I simply couldn’t leave myself unprotected any longer.
I’ll still of course keep a development device jailbroken on 12.1.2 for all of the reasons. It was a wonderful experience, only slightly beta. I appreciate all the hard work by everyone in the scene. I think i am going hate seeing the home bar again the most.
* web pages are often sandboxed separately from the app itself. Some might argue that a webpage would first have to escape the sandbox before it could escalate privileges. this is true, but i would respond that sandbox escape is just another form of privilege escalation, only one level down. There are also over a dozen webkit fixes in this update.









